In this article we will find out if Base32 is encryption or not, we will see if we can say encrypt or decrypt for Base32. We will explain what exactly Base32 is and explain the differences between encryption, encrypt, encoding and decrypt.
Is Base32 an Encryption?
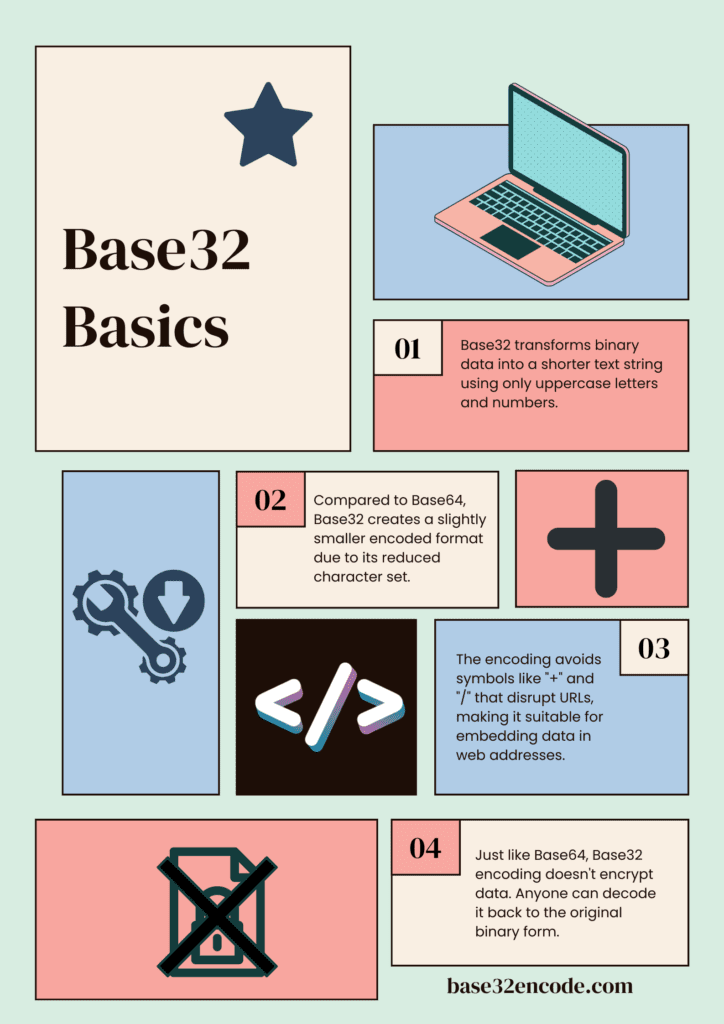
No, Base32 is not an encryption method. It’s a binary-to-text encoding scheme that is used to convert binary data into a string format that can be easily transmitted or stored.
Encryption, on the other hand, is a process of converting data into a format that is unreadable without a decryption key. While both encoding and encryption transform data into a different format, the key difference is that encoded data can be easily reversed or decoded, while encrypted data cannot be decrypted without the correct key. So, Base32 is an encoding scheme, not an encryption method.
What is Base32?
Base32 is a binary-to-text encoding scheme that allows binary data to be represented in a human-readable format. This encoding method uses a set of 32 different characters, typically comprising digits (0-9) and a selection of uppercase letters (usually A to Z), excluding easily confused characters like ‘1’ and ‘I’ or ‘0’ and ‘O.’ Base32 serves as a way to convert binary data, which computers use, into a format that can be easily read and handled by humans.
At its core, Base32 is based on the principle of grouping binary data into sets of 5 bits, which can represent 32 different values. Each 5-bit group is then mapped to one of the 32 predefined characters. These characters are carefully chosen to ensure they are easily distinguishable, making it unlikely for them to be misinterpreted or corrupted when transmitted or copied.
Why Do Many People Think Base32 is Encryption? Encryption vs Encoding
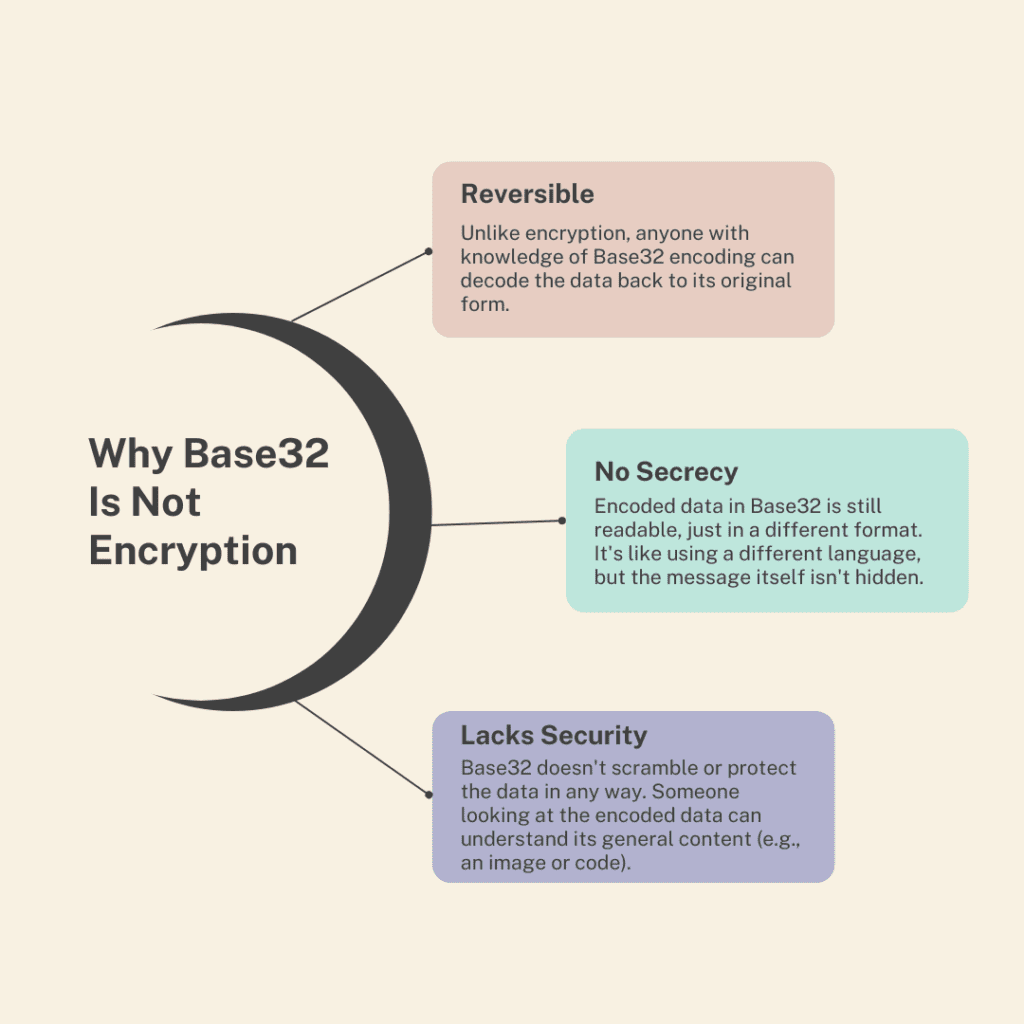
One of the primary factors contributing to the perception of Base32 as an encryption method is the ambiguity surrounding the term “encoding.” In everyday language, the term “encoding” can be easily confused with “encryption.” To make matters more confusing, encoding and encryption both involve converting data into a different format, which adds to the misunderstanding.
The misconception about Base32 arises from its use in contexts where data needs to be kept secure, such as representing cryptographic keys. People may mistakenly assume that Base32 is an encryption method when they encounter Base32-encoded data related to cryptography. However, Base32 is simply used to represent binary cryptographic keys in a human-readable format.
Base32 is commonly used in applications where data protection and integrity are crucial. For example, it is utilized in data checksums to verify that data has not been altered during transmission. Although Base32 is primarily used for data representation, not data protection, its emphasis on data security can lead some to mistake it for encryption.
It’s important to understand the fundamental distinction between encoding and encryption:
- Encoding: Encoding is the process of converting data into a different format that is easily readable by both humans and machines. It does not involve the use of algorithms or keys to protect data. Base32 falls under this category.
- Encryption: Encryption, on the other hand, is the process of transforming data into a format that is unreadable without the use of a decryption key or algorithm. Its primary goal is data protection and security.
| Feature | Encryption | Encoding |
|---|---|---|
| Purpose | Protects data confidentiality (makes it unreadable) | Represents data in a different format (for storage, transmission) |
| Reversibility | Requires a decryption key to get original data | Decodable back to original data using the same encoding method |
| Security | Encrypted data is secure (unless key is compromised) | Encoded data is not secure, anyone can decode it |
| Character Set | Often uses a wider range of characters | May use a specific character set depending on the encoding method |
| Examples | AES, RSA | Base32, Base64, ASCII, URL encoding |
What is Encryption?
Encryption is a multi-step process that starts with plaintext, the original data that needs protection.
The following are the primary steps involved:
- Key Generation: Encryption relies on cryptographic keys, which are essentially complex mathematical algorithms. These keys determine how the plaintext is transformed into ciphertext (encrypted data) and vice versa. Key generation is a critical part of the process.
- Data Transformation: In this step, the plaintext data is subjected to various encryption algorithms, such as symmetric or asymmetric encryption. Symmetric encryption uses the same key for both encryption and decryption, while asymmetric encryption involves a pair of keys, a public key for encryption and a private key for decryption.
- Creating Ciphertext: The result of the data transformation step is ciphertext, which appears as random and unreadable data to anyone who does not possess the correct decryption key. This ciphertext is secure and can be safely transmitted or stored.
- Secure Transmission or Storage: Encrypted data can be safely transmitted over networks or stored on devices without the risk of exposure. Even if intercepted, the ciphertext is virtually impossible to interpret without the decryption key.
Encryption serves several critical purposes in today’s digital world:
- Data Privacy: It ensures that sensitive and confidential information remains protected from unauthorized access. This is vital for personal data, financial transactions, and communication.
- Data Security: Encrypted data is resilient against cyberattacks, as the ciphertext is difficult to decipher without the proper keys. This makes it an effective tool in preventing data breaches.
- Regulatory Compliance: Many regulations and standards, such as GDPR and HIPAA, require the use of encryption to safeguard data and maintain compliance.
- Secure Communication: Encryption is essential for secure communication, particularly over the internet. It protects emails, online banking transactions, and more.
- Data Integrity: Encryption also helps verify the integrity of data by detecting any unauthorized modifications during transmission or storage.
There are various encryption methods, including:
- Symmetric Encryption: This type uses a single key for both encryption and decryption and is known for its speed and efficiency.
- Asymmetric Encryption: Asymmetric encryption employs a pair of keys, with one used for encryption and the other for decryption. It’s commonly used for secure communication and digital signatures.
- End-to-End Encryption: This form of encryption ensures that data remains secure from the moment it is sent by the sender until it is received by the intended recipient.
What Are Encrypt and Decrypt?
Encryption is the process of converting plaintext or readable data into an unreadable format known as ciphertext. This transformation is achieved using a mathematical algorithm and a secret key. The primary goal of encryption is to protect sensitive data from unauthorized access. Here’s how it works:
- Plaintext: The original, human-readable data that you want to safeguard.
- Encryption Algorithm: This is a mathematical formula that transforms the plaintext into ciphertext.
- Encryption Key: A secret key is used to control the encryption process. Without the correct key, it is virtually impossible to decipher the ciphertext back into plaintext.
- Ciphertext: The result of the encryption process. It appears as seemingly random data and is secure from prying eyes.
Encryption is commonly used to secure data during transmission or storage. For instance, when you provide your credit card information for an online purchase, it is usually encrypted before being sent over the internet to safeguard it from interception.
Decryption is the reverse process of encryption. It involves taking the ciphertext and converting it back into plaintext, making the data readable and accessible once again. The decryption process requires the correct decryption key that matches the one used for encryption. Here’s how decryption works:
- Ciphertext: The encrypted data that you want to make readable.
- Decryption Algorithm: This is the mathematical procedure that reverses the encryption process, converting the ciphertext back into plaintext.
- Decryption Key: The secret key used to control the decryption process. It must match the key used for encryption.
- Plaintext: The result of the decryption process. It is the original, human-readable data.
Decryption is necessary for authorized parties to access and use encrypted data. For instance, when logging in to your email account, the server decrypts your messages to display them in a readable format after you provide the correct credentials.